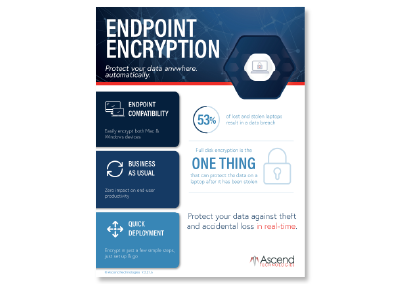
Endpoint Encryption
Proactive Data Protection With Synchronized Encryption
Encrypt content as soon as its created. And with the encryption always on, you can enjoy seamless secure collaboration. Synchronized encryption proactively protects your data by continuously validating the user, application, and security integrity of a device before allowing access to encrypted data. This method of always-on protection goes everywhere your data goes, making it the most comprehensive data security solution on the market.
Compatibility
Encrypt Mac or Windows
we play nice with your devices
Business as Usual
Open, edit, or share files
as you normally would
Simple Deployment
Seamless over-the-air
deployment
%
of lost and stolen laptops result in a data breach
Intelligently protect your data against
theft and accidental loss in real-time
Why choose ascend?
Our encryption solution has the ability to intelligently protect your data against theft. It automatically encrypts your content, and the content stays encrypted even when it’s shared or uploaded to a cloud-based, file-sharing system.
Our encryption service continuously validates the user, application, and device integrity. If your data ever ends up in the wrong hands, Encryption renders the information unusable; the files remain encrypted and unreadable.
Benefits of Endpoint Encryption
& compliance
QUICK AND EASY DEPLOYMENT
Ascend’s Device Encryption manages Windows BitLocker and macOS FileVault native device encryption. There is no server to deploy and no need to configure backend key servers.
We’ll deploy and start securing data in minutes with a simple, cloud-based installation agent. Plus, we can easily secure data on remote laptops.
SIMPLIFIED REMOTE DEVICE MANAGEMENT
Maintain compliance and protect your data without disrupting users in the event of a lost device or forgotten password. Improve protection for remote devices with our user-centric solution that makes it easy to enable device encryption and protect multiple devices from anywhere.
COMPLIANCE
As a part of compliance requirements, you will likely need to be able to verify which computers in your organization are encrypted.
In the case of lost or stolen laptops, you’ll also need to provide proof that these missing devices are encrypted. Ascend helps you comply with data protection regulations with detailed reports and audits.
Continue Exploring
eBook: Cybersecurity Basics

Blog: 5 Easy Ways to Improve
Your Cybersecurity at Work
Datasheet: Endpoint Encryption