Cloud-based software tools are incredibly useful and are practically a must-have for any business that wants to be competitive. Nevertheless, cloud-based systems aren’t without their risks. Unfortunately, many companies assume that their data is always safe in the cloud. How can you protect your valuable data and operations in the cloud? Consider some of the vulnerability management methods your cloud systems can use to mitigate potential threats.
How Do Cloud-based Tools Affect Your Cyber Vulnerability?
The cloud has changed where and how company data is stored and accessed. Rather than using traditional servers in the office that run bespoke programs, cloud-based systems store data in various data centers around the world. This means that attackers cannot focus on the physical infrastructure itself. Instead, they have to try to acquire your associates’ credentials in order to access your cloud platform, where they can steal whatever data they please.
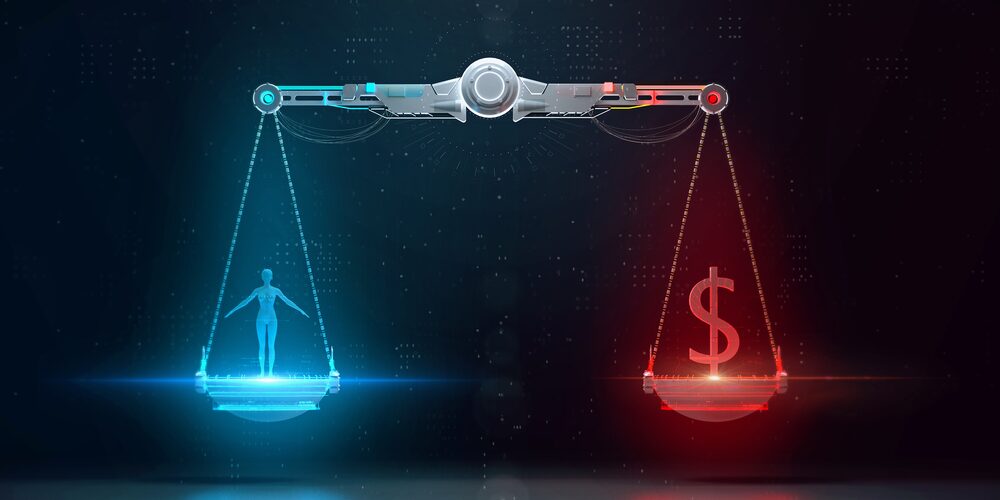
If a criminal gets one of your associate’s credentials, they will have the same level of access as that individual. They could download all of the data they find on your cloud platform, or even delete valuable data. Given the penalties that your company could face if your clients’ personal information were leaked or lost, it’s best to proactively manage your cybersecurity to prevent attacks from happening in the first place. So, what should you do to prevent these attacks?
Cloud Risks That Require Vulnerability Management
You generally don’t have to worry about hardware-based attacks when it comes to cloud platforms. Since data is distributed across many data centers, which are highly secure, criminals cannot simply hack into cloud servers and steal your company’s data the way we often see it depicted in Hollywood. Instead, attackers look to steal employee access credentials, namely logins and passwords. This approach accounts for over half of the data breaches analyzed by IBM’s annual report.
Criminals can gain access to your access credentials in several ways. The primary method is to use a phishing attack. However, malware is also used to steal information. Consider how these two attack methods work and how you can prevent them.
Phishing Attacks
Phishing attacks work by trying to trick your associates into giving up their access credentials. The majority of these attacks use deceptive emails. They may even go so far as to buy a domain with your company’s name, perhaps the .co version, which at a glance won’t seem unusual.
The emails tend to be alarmist in nature to provoke a quick response. For example, they might claim you’ve been hacked and need to reset your password. Once you submit your old password to the decoy server, the phisher now has your information and can access your account in the cloud.
Malware Attacks
Malware attacks also typically occur via email. However, instead of trying to convince the reader that the email comes from the company, these emails include seemingly innocent attachments that actually contain malicious code. For instance, you might see a PDF that claims to be a purchase order, an invoice, or a proposal for services. Once the file is opened, it plants malware on the user’s computer.
Malware can monitor keystrokes and report them back to the attacker. Once you log into your cloud platform, they have your access credentials. Other methods wait for you to log into your platform and then duplicate your session remotely. This is what happened to the largest tech-advice media company, Linus Tech Tips. If even they can fall victim, so can you. What can you do to prevent these types of attacks?
How to Manage Cloud Access Control to Reduce Vulnerability
The key to protecting your cloud-based systems is to use a second layer of security. You cannot rely only on usernames and passwords, even if you change them regularly. The second form of security will require your associates to confirm their login using another device that only they should have on their person. Even if your access credentials are stolen, this second layer of security will keep criminals from entering your platform.
Best of all, these methods do not require much effort to use. It’s always important for security to be simple. If extra security methods make it hard for your team to access its cloud platform, they will resent it, rather than appreciate it. We recommend using two-factor authentication and potentially using physical security keys for maximum protection. Here’s how they work.
Always Use Two-Factor Authentication (2FA)
Two-factor authentication, or 2FA, is one of the most useful tools for additional security. With 2FA, your associates must confirm their login on their own personal device, usually their cell phone. Once a login is detected, a notification is pushed to the device registered with that user’s account. They can confirm or deny the login accordingly.
If a user receives a notification when they aren’t trying to log in, that’s a sign that their credentials have likely been stolen. They can then create a new password and return to normal operations. However, it’s also important to train your staff to use 2FA properly. Some criminals will make numerous login attempts to push many notifications, hoping to wear out the user and get them to simply accept the notification to make them stop.
Physical Keys
Another method you can consider are physical keys that provide a second, or even third factor for authentication. Physical keys like Google’s Titan Security Key plug into the user’s device and authenticate their session when they attempt to log in. It may not be ideal to have everyone use a physical key, though. Consider using these devices specifically for the individuals in your organization who have root-level access, or those who can access all of the company’s data.
These extra methods of security can be complemented by other tools like email monitoring and network activity monitoring. Managed IT service providers can help you develop a personalized security solution that covers every potential attack vector. Contact us at Edafio to schedule a meeting with our experts and design a security solution for your company.