Whether you’re in engineering, healthcare, manufacturing, retail, or sales, every industry has its unique way of communicating. Different professions and industries apply selected terms and phases known as lexicons.
The lexicon is simply the vocabulary of a language or branch of knowledge that allows professionals in that field to communicate seamlessly. While some terms and lexicons are easily understood, like PTO, OOO, and COB, others are sophisticated and less understood, such as EPS, AR, AP, FTE, and P&L.
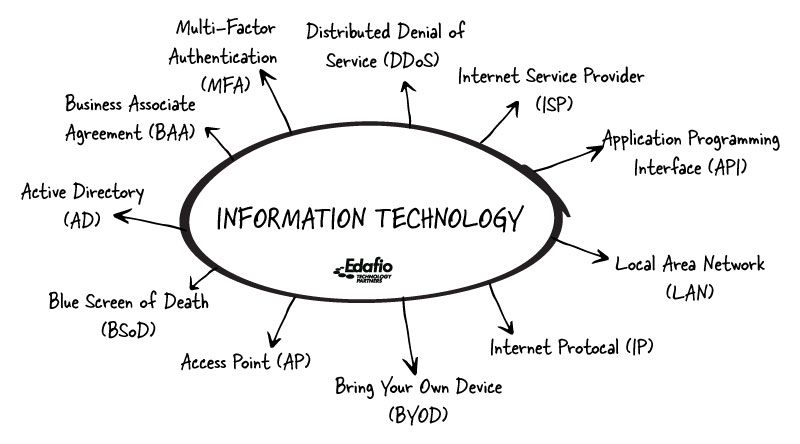
The IT world is no different. But, since our world is somewhat specialized, our acronyms are not as widely understood.
At Edafio Technology Partners, we use a lot of technology-related acronyms and abbreviations, and as IT insiders, we understand and we can help. So we decided to put together a list of IT acronyms we frequently use and what they mean in easy-to-understand language.
Knowing these acronyms will give you a leg up when talking with your IT support team and make you more confident in your interactions with them.
So the next time your IT person drops any of these in a conversation, you can confidently nod your head, agree and say, “I know what it is.”
What are the most common IT abbreviations?
MFA
MFA is a shorthand for multi-factor authentication. The MFA is a security measure that requires users to provide multiple forms of authentication before granting access to a protected system, network, or device. MFA requires users to enter more than one — typically two pieces of information to access an account. The first authentication is the password; the second can be a text message sent to your linked phone number or conveyed to a different email address. Example include:
Knowledge factors are something you know: Passwords
Possession factors apply to things you own, such as one-time passcode sent to your smartphone or provided via a token
Inherence factors use your biological characteristics like fingerprint scans.
AP – ACCESS POINT
An Access Point (AP) is network hardware that connects your wireless devices to your wired network. The AP links to a switch or router by an Ethernet cable and is the hub your wireless device connects to your wired Local Area Network (LAN) (we’ll talk about it too).
So the AP projects the Wi-Fi signal in a selected area. The next time you need a Wi-Fi signal in another location, such as the company picnic area, you could run an ethernet cable and install an AP.
IP- INTERNET PROTOCOL
IP stands for Internet Protocol, but what does it mean?
IP is a set of rules for routing data to travel across networks and reach the right destination. It is also the central communications protocol in the Internet protocol suite. When spanning across a network such as the Internet, data is broken up into small pieces called packets and attached to each packet is the IP information that helps routers send packets of data to the correct address. Each domain or device that is connected to the Internet has a unique IP address, and packets are directed to valid IP addresses using the IP information.
ISP- INTERNET SERVICE PROVIDER
An Internet Service Provider is an organization that gives you access to the Internet.
You need routing equipment, networking, and telecommunications to connect your device to the Internet. Technically, an ISP lets users “rent” the special equipment needed to establish an internet connection. ISPs make Internet access possible by routing Internet traffic, resolving domain names, and maintaining the network infrastructure.
LAN- LOCAL AREA NETWORK
A Local Area Network is a computer network that interlinks devices within a limited physical location, such as a home or office. It can be as significant as a large network with thousands of users and devices or as small as a home network with one user.
A typical office LAN comprises switches, APs, cables, routers, and other components, which enable the devices to link to internal servers and other LANs. LANs allow the connected devices to use a single internet connection, such as using shared printers, sharing files, and accessing the connected devices.
API
The API refers to the Application Programming Interface. The API software allows two different systems or platforms to communicate and exchange information seamlessly. Think about a mobile app; that is an API.
For instance, flights on an aggregator like Skyscanner rely on APIs to communicate with the airline’s website. The API is the platform that hosts information such as flight routes, baggage options, ticking processes, and pricing.
So, when users search on the Skyscanner, the API takes their query to the airline’s website, obtains a detailed response to their requests, and sends them the final results about their flight.
So, the API is a critical component in inter-system communication, automation, and interoperability.
BYOD
This is a shorthand for ‘Bring Your Own Device.’ This concept allows employees to use their devices for professional and work purposes. BYOD is a popular term in small companies because it allows employees to bring their devices, allowing the enterprise to free up capital that would otherwise be tied to purchasing devices.
DDoS
This refers to Distributed Denial of Service DDoS, which is a malicious attempt to delay or block the traffic of a computer, network, or server by sending fake or flooded traffic. Distributed denial of service DDOS is usually used by attackers when they want to target specific servers or machines.
In this attack, the hacker or attacker creates fake traffic on your route to prevent genuine traffic from reaching your servers, service, or network.
DDOS attacks are initiated by flooding the target’s network or servers with fake traffic, interrupting the genuine flow of real traffic. These attacks are particularly effective as they leverage a network of targeted computers and IoT devices.
After seizing and gaining control of many computers, the attacks infect the computers with malware and use the infected devices as a bottleneck to launch further attacks.
So, DDOS attacks are critical cyber threats businesses must always look out for. Deploying sound cybersecurity practices through the help of trusted cybersecurity-managed service providers is one of the best ways to remain protected against unprecedented cyber threats.
AD
The AD refers to active delivery. Active delivery is a model of delivering IT support services based on the results obtained from constant evaluation and monitoring of a particular IT environment. The AD approach makes it possible to diagnose IT issues early on before they become detrimental to business operations.
So, enterprises deploying active delivery techniques are best suited to obtain actionable results on underlying IT issues, thus saving themselves from unprecedented system failures and compromise.
BAA
A BAA is a Business Associate Agreement. The HIPAA regulations call it a Business Associate Contract, but they are the same thing.
BAAs satisfy HIPAA regulations and create a bond of liability that binds two parties.
If one member violates a BAA, the other has legal recourse. If there’s no BAA, or it’s incomplete, or if it gets violated, then both associates may find themselves in hot water with HIPAA and other FDA regulations.
BSoD
You probably have heard about the ‘Blue Screen of Death.’ This is a disastrous window error officially known as a ‘blue screen’ or a ‘stop’ that appears as a fully blue screen right before your desktop or laptop. However, do not panic, as BSoD is never a fatal error. It can always be diagnosed or troubleshooted.
CMMC
The United States Department of Defense developed the cybersecurity maturity model certification as a comprehensive framework. This CMMC was developed to measure the commitment and ability of government contractors (and sub-contractors) to keep the information used within the U.S Defense Industrial Base safe from cyber threats.
Thus, the Cybersecurity Maturity Model Certification is a framework to ensure critical life-threatening information and data is kept safe by contractors and sub-contractors working with the United States Department Base.
DSS
Also called a Decision Support System, the DSS is a system that collects, arranges, and scrutinizes business data such as sales, inventory, and finance information for use in organizational decision-making.
Organizations understand that humans are limited in their capacity to collect huge sets of data, correlate, and draw meaningful insights from such sophisticated quantitative variables.
So, the decision support system DSS uses artificial intelligence and automation to collect, organize, and analyze data for informed decision-making. The ability to collect consumer, market and business information is being sought worldwide, making DSS a critical metric in organizational decision-making.
Edafio Technology Partners – Simplifying Managed IT
Managed IT is an evolving sector that delivers IT support services to small and medium-sized businesses at just a fraction of the cost. By working with a managed service provider, you access cybersecurity services, network monitoring, IT consulting, and cloud computing services – all as a package. You can also choose which solutions you want to be embedded in your IT environment.
You do not have to run an internal IT department and need help with emerging operational, investment, and administration costs. With managed IT services from trusted providers like Edafio Technology Partners, you’re assured of quality IT services that meet your changing IT needs.
Contact Edafio Technology Partners to explore various IT solutions.